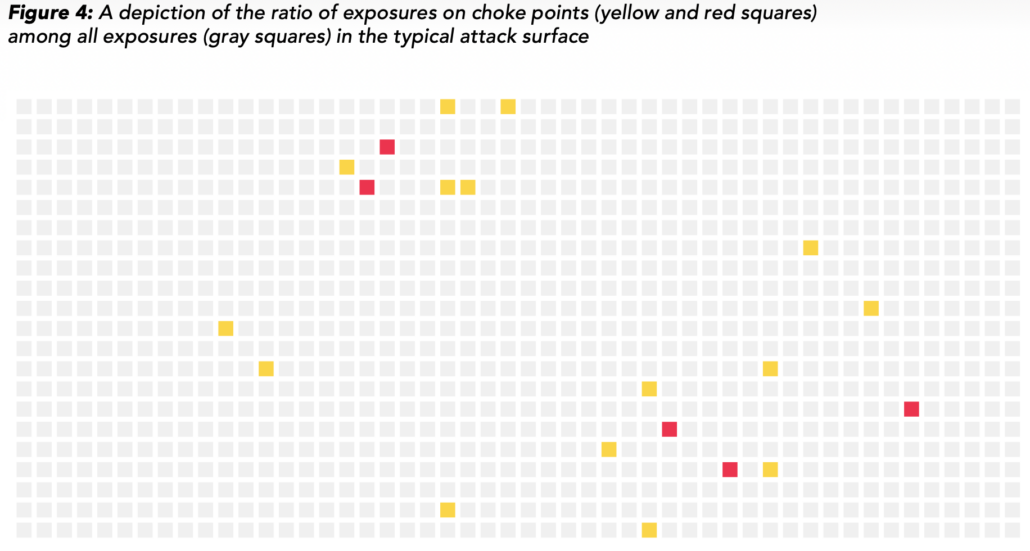
/wp-content/uploads/2023/05/Screenshot-2023-05-17-at-9.20.48-AM.png
980
1832
Wade Baker
/wp-content/uploads/[email protected]
Wade Baker2023-05-25 12:15:502025-08-18 11:15:26Visualizing the Value of Attack Path Choke Points for Prioritization
/wp-content/uploads/Arete-Reining-In-Ransomware_Page_01.png
1584
1224
John Sturgis
/wp-content/uploads/[email protected]
John Sturgis2022-10-14 08:13:112024-11-19 12:35:03Finding (san)Key Protections Against Ransomware
/wp-content/uploads/mitigating-ransomware-cover-pdf.jpg
1408
1088
John Sturgis
/wp-content/uploads/[email protected]
John Sturgis2022-06-10 13:38:562025-08-18 11:15:25Paying Ransoms & Information Asymmetry
/wp-content/uploads/cybersupplychain.png
302
705
Wade Baker
/wp-content/uploads/[email protected]
Wade Baker2022-01-26 12:09:542024-11-19 12:35:04Bridging 18y Studying Cyber Risk in Supply Chains
/wp-content/uploads/IRIS-Tsunami-cover-1.png
1848
1428
John Sturgis
/wp-content/uploads/[email protected]
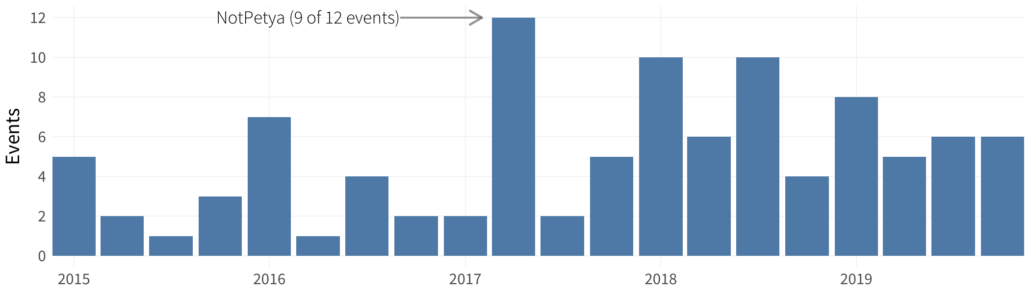
John Sturgis2021-10-26 09:24:352024-11-19 12:35:05IRIS Tsunami - Lessons from 50 of the largest multi-party cyber incidents
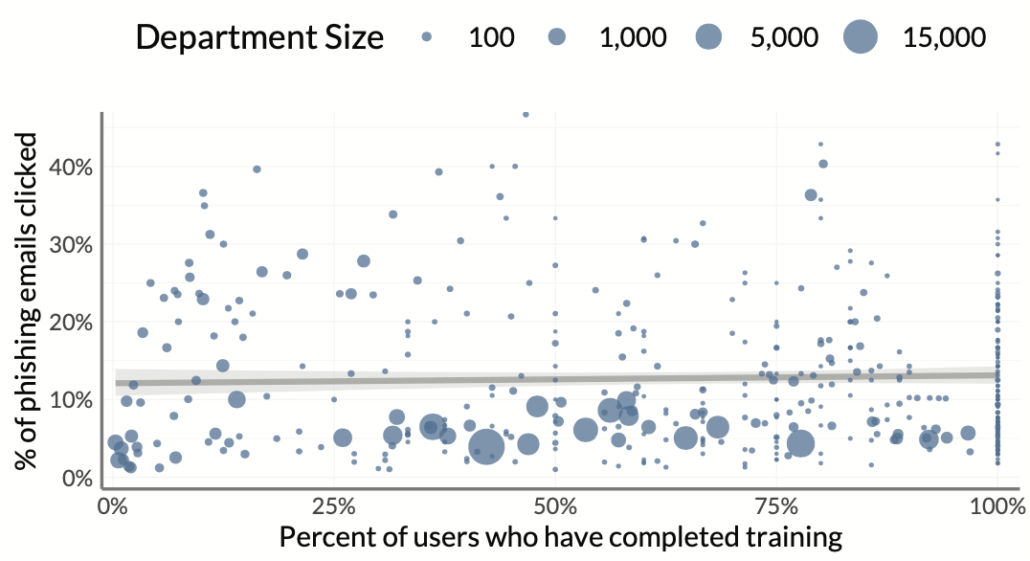
/wp-content/uploads/elevate-training-org.png
586
1076
Wade Baker
/wp-content/uploads/[email protected]
Wade Baker2021-06-28 09:40:532024-11-19 12:35:05Salving Human Risk in Cybersecurity
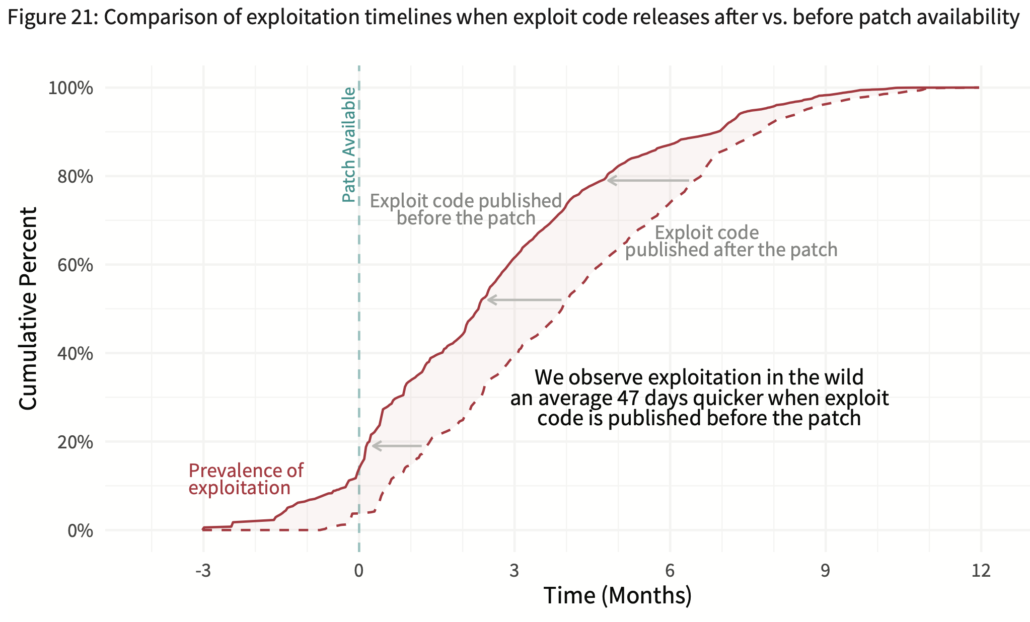
/wp-content/uploads/p2pv6fig21.png
1160
1920
Wade Baker
/wp-content/uploads/[email protected]
Wade Baker2021-01-21 08:00:222025-08-18 11:15:23I Once Called Vuln Researchers NVPs; Are They MVPs Instead?
/wp-content/uploads/soss11-fig16.png
1114
1794
Wade Baker
/wp-content/uploads/[email protected]
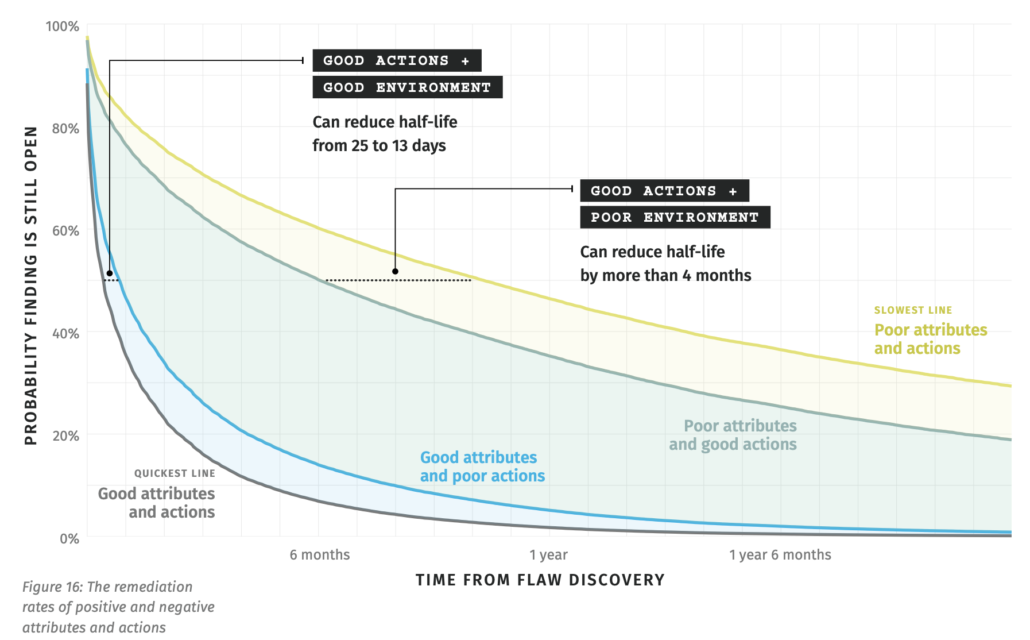
Wade Baker2020-12-10 12:00:532024-11-19 12:35:16What Matters More in Software Security - Nature or Nurture?
/wp-content/uploads/figure05.png
600
2100
David Severski
/wp-content/uploads/[email protected]
David Severski2020-11-20 16:03:542024-11-19 12:35:16IRIS 20/20 Xtreme Webinar - Audience Questions
/wp-content/uploads/p2pv6-fig20.png
1042
1892
Wade Baker
/wp-content/uploads/[email protected]
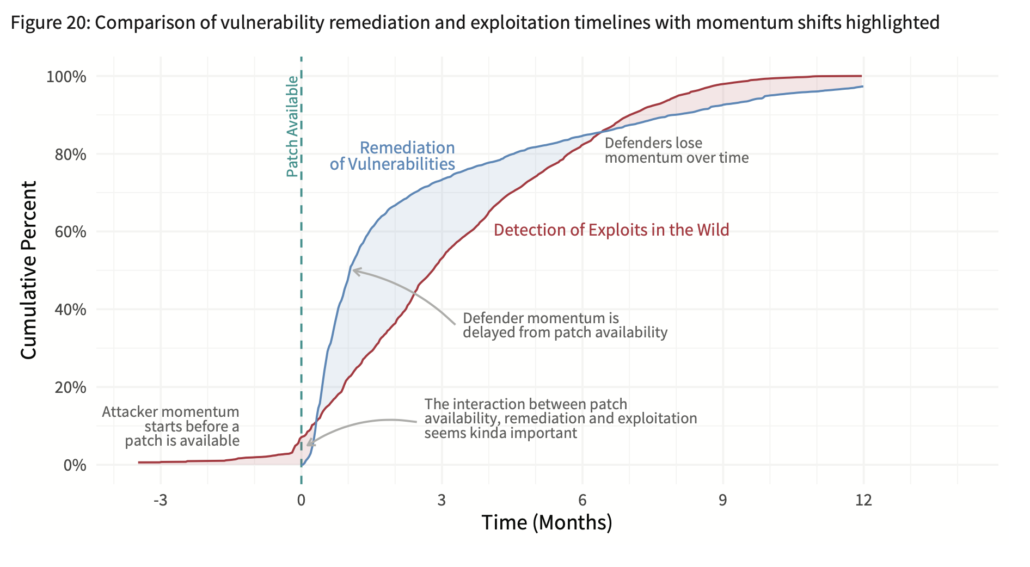
Wade Baker2020-11-19 11:22:062024-11-19 12:35:17Who Has the Advantage - Attackers or Defenders?
© Copyright 2026 Cyentia Institute
Scroll to top