Last week I participated in a webinar with Advisen and a panel of industry experts on estimating costs from breaches more accurately. Our focus was our recent IRIS 20/20 publication and the key findings from that report. Hundreds of attendees join the all too brief discussion and we didn’t have time to address all of the audience questions. We’ve compiled these into a list of FAQs for readers!
If you missed out on attending the webinar and would like to get more context into these questions, a recording is available via Advisen’s website. Thank you to all the attendees and a special thanks to everyone that raised questions!
Q: Where can I find a copy of the report?
A: The IRIS 20/20 report is freely available for download, with no registration required, at https://cyentia.com/iris.
Q: Does your analysis use any non-public data? Is the raw data available for download?
A: All of our loss data is from publicly available sources and compiled into the Advisen Cyber Loss Feed. While the data is public, the curated feed is a subscription product available from Advisen.
Q: Are there examples of breaches that resulted in the end of companies as an ongoing concern?
A: Our raw data set from Advisen does include information, where available, about subsequent bankruptcies in firms that experience cyber events. We have not yet conducted research in this area.
Q: What is the largest breach in the data set?
The largest financial loss in our sample is the Epsilon Data Breach of 2011 at 4 Billion USD. The largest incident by number of records involved is the Yahoo Inc event of 2013-2014, at 3.5 billion records. Examining these extreme events is an area we are eager to pursue and have a call for sponsors.
Q: Does the data include events that impact availability and integrity elements in additon to just those affecting confidentiality?
A: Yes! Any publicly discoverable event that also had some valuation for economic loss is included. If an event resulted in lawsuits, response costs, or other types of verifiable economic losses, they are included here in our data set.
Q: Does the report cover all sectors of the economy? Where is the telecom sector?
A: We used the NAICS classification scheme to group affected firms into top level sectors. The telecommunications sector falls under NAICS code 62, the Information sector. In the future, we may examine smaller sub-sectors or specific industries.
Q: Does frequency vary based upon type of breach?
A: We looked at publicly disclosable, non-privacy, events that impacted the confidentiality, integrity, or availability of cyber systems. The Advisen data does contain some high level buckets of the type of event, but this information is difficult to obtain from public sources such as used by Advisen. We’re continuing to look for additional data sources to help get further information into the root causes of breaches for future work.
Q: Is the frequency and loss model available online?
A: We’ve published segmented discrete values for both frequency and losses and are actively looking for sponsors to continue to develop an open model based on this work.
Q: What information types are included in these loss records?
The record types involved in losses are varied, including but not limited to personally identifiable information (PII) and company sensitive information. The vast majority of losses in our data set are from loss of some form of personal information.
Q: How do regional legislation efforts (i.e. GDPR, CCPA, etc.) change loss amounts?
A: For a reliable denominator for the number of firms in various sectors of the economy, we focused on firms with a headquarters location in the United States. Many US firms also have international presences and are therefore in scope for legislation such as GDPR. With the global nature of many firms, we choose not to focus on regional differences for this initial report, but it is a topic we hope to come back to for future work!
Q: How does this compare with the Ponemon/IBM Cost of Breach study?
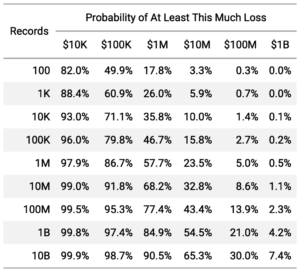
A: The Cost of Breach study is based upon a survey methodology of corporate professionals. The cost per record number from that study is a single value for a small range of loss types. As tempting as that single number is for estimating potential losses, we show that use to be vastly inaccurate. Our advise is simple: Do not use a single cost per record number for estimating losses. IRIS 20/20 provides estimates that are very easy to use that deliver much more accurate results. Table 4 from IRIS 20/20 (presented below) is a quick reference to replace the flat cost per record values with more accurate estimates.
Q: Do the loss amounts include internal response costs? Do losses include opportunity costs, such as lost business?
A: The Advisen cost values include publicly verifiable losses, such as found in SEC filings and legal proceedings. Estimates on internal response costs that would be found in public disclosures are included.
Q: Why are there no error bars for the frequencies and loss values?
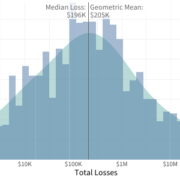
A: For the likelihood of a breach in a year, our probabilities calculated based on the total observed population (Fortune 1000 or total number of US firms in a particular sector) not a sample, so the reported proportions are not estimates, but rather known statistics. We have chosen to present the entire distribution of values for our loss statistics (see Figures 9 and 10). Future research may present parameterized representations of these distributions from which confidence intervals of any estimated statistics could be derived.
Q: Can loss data be separated based upon the types of damages (legal, response costs, etc.)?
A: Our data partner on this project, Advisen’s Cyber Loss data feed, does include losses broken out by specific type where available. Getting reliable loss values at this level is challenging, but not impossible. For this analysis, we focused on overall economic impact to answer the question of “how much” we see a lot of organization’s ask. We’d love to delve further into types of losses in future work, with a research project on extreme losses already lined up and seeking sponsors — See our call for sponsors!
Q: Is there correlation on the efficacy of cyber security programs with breach information?
A: An excellent question and the Holy Grail of loss research! We do not have data to match cyber control programs and their efficacy with loss records.
[/av_textblock]






Leave a Reply
Want to join the discussion?Feel free to contribute!