New Research: Close Encounters of the Third & Fourth Party Kind Subsector Reports
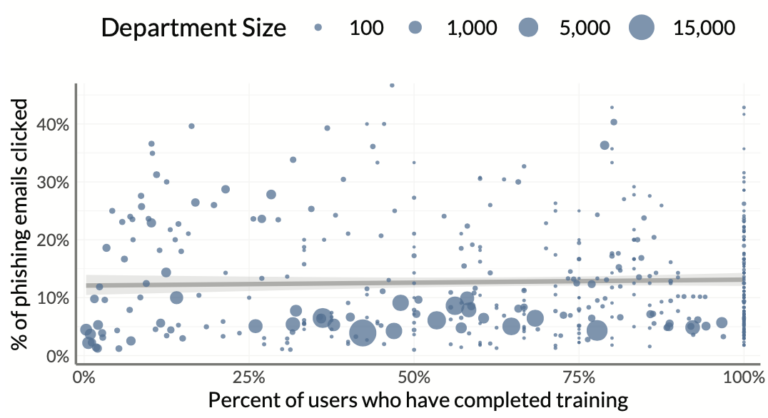
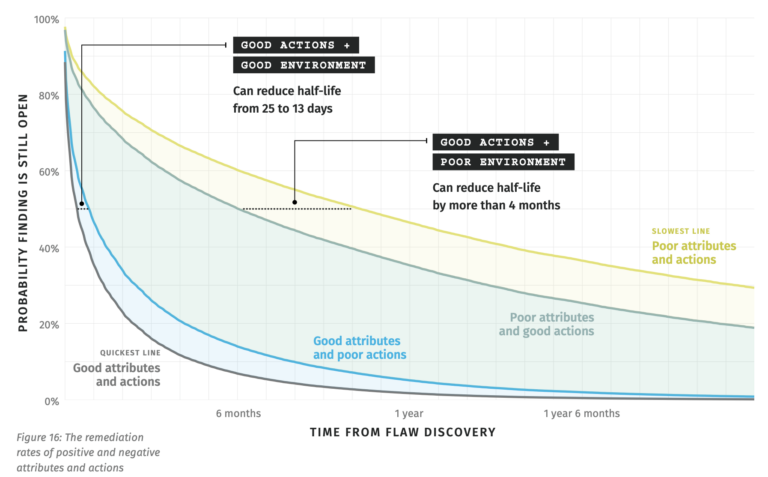
In today’s interconnected digital landscape, organizations are only as strong as their weakest link when it comes to cyber defenses. The alarming headlines of breaches originating from third and fourth parties serve as a constant reminder of this truth. Finance firms, in particular, understand the risks associated with these “close encounters.” Read on to learn…