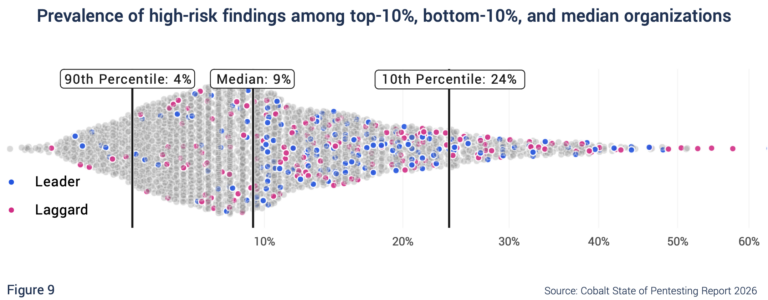
High Performance in a High-Risk Environment?
Cyentia Institute collaborated with Cobalt on the latest State of Pentesting Report, which was released last week. The thing I found most interesting in this edition is the organization-level performance benchmarks we derived for the first time. We measured 4 key metrics and compared them across thousands of organizations: This essentially answers “How exposed are…