Track exploits, prioritize remediation
Cyentia’s product, Exploit Intelligence Service, leverages advanced machine learning capabilities to identify and track exploits released on GitHub and other sources, providing you with a probable prediction of the likelihood that the GitHub material is an exploit. Discover how you can cut down the manual effort of inspecting every repository to reduce your cyber risk and protect your bottom line.
Stop Guessing,
Start Knowing
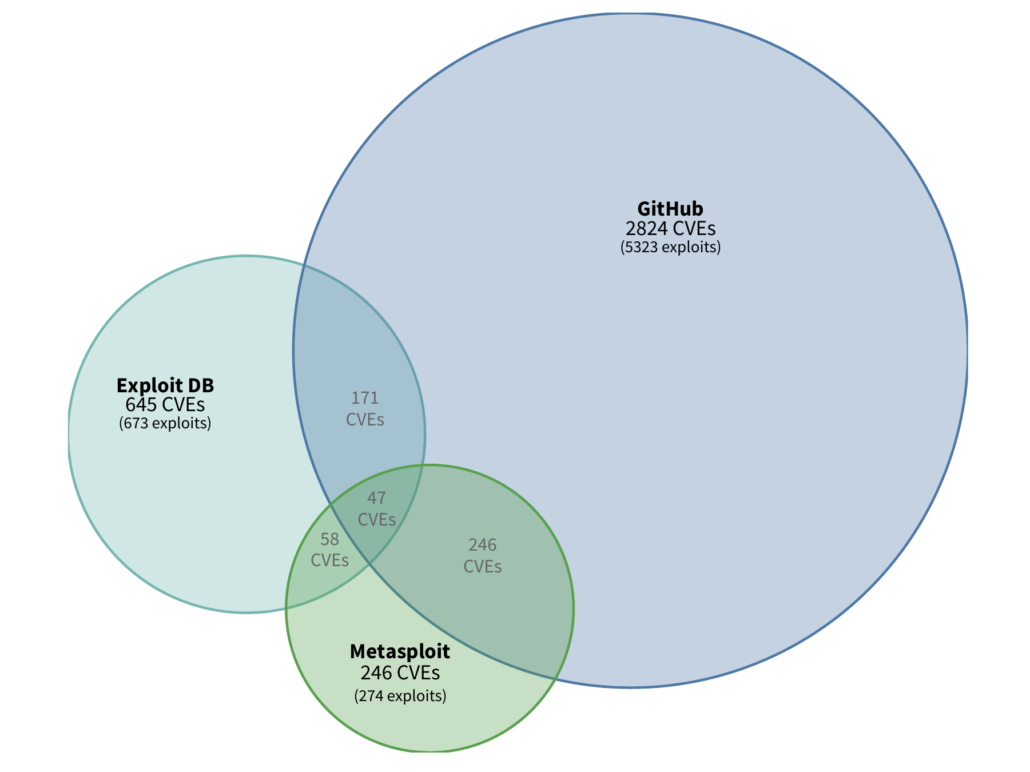
There is a strong relationship between publicly available exploit code and actually seeing an exploit used in the wild. In fact, 6x the number of firms are reporting exploitation activity and observing 15x the volume of exploitation attempts (Source: Kenna Security). when an exploit is published vs not. What’s more, publishing appears to be shifting away from forums like ExploitDB and towards GitHub—making it increasingly difficult to find published exploit code. If exploits aren’t identified early, they can result in costly breaches and reputational damage for organizations. No organization is immune. At Cyentia, we knew there had to be a more proactive and precise way to identify and track exploits.